Freestate Electric is dedicated to protecting our customers’ and employees’ personal information. To that end, we have several systems and procedures in place to safeguard our information and networks. Diligent users are our first line of defense. Please check this page regularly for updated information and training links to stay up to date on current threats.
Phishing Attacks
What is a Phishing Attack:
Phishing is a type of online scam that targets consumers by sending them an e-mail that appears to be from a well-known source – an internet service provider, a bank, or a mortgage company, for example. It asks the consumer to provide personal identifying information. Then a scammer uses the information to open new accounts or invade the consumer’s existing accounts.
Here are the key indicators that an email or Link may be part of a phishing attack
- The Message Contains a Mismatched URL
One of the most obvious signs of a phishing attack and a malicious piece of content is that the content doesn’t match the URL. But because many people are becoming wise to this type of clue, attackers are now changing the URL to match their message. However, in some cases, users will find that if they mouse over the URL, the URL doesn’t match the text link.
This is a significant sign of a scam and should be reported.
- The URL Doesn’t Match the Domain
Another trick employed by cyber criminals is to use a URL that doesn’t match the domain of their site. For example, they might use the name of a legitimate company such as Apple or Microsoft in order to get the user to click on the link and go to their malicious content. The name of the legitimate company will be the main domain, and then the fraudulent company will be a child domain within the link. In this example, a user might see something like “www.apple.scamwebsite.com”.
Example: The link below says www.freestateelectric.com, but if you move the mouse over it the link it is really trying to send you to is www.microsoft.com.
- The Sender of the Communication Doesn’t Appear Legitimate
In some cases, it’s possible to determine whether the communication involves a phishing scam simply by looking at the sender of the information. While phishing attackers are becoming better at disguising their address, there are still small differences between legitimate communications and fraudulent communications in terms of the email address of the sender.
For example, the common PayPal phishing scam involves senders using Gmail or Hotmail email addresses, and not an original PayPal address. We have seen an extra “e” in our domain such as @freestateeelectric.com and even seen the “L” replaced with an “I” so it looks like @freestateeIectric.com.
- The Content Contains Poor Spelling and Grammar
While most people aren’t perfect when it comes to spelling and grammar, the vast majority can spot misspelled words and poor English if they look closely at the content. But many still miss this vital clue in addressing phishing attempts. In a legitimate piece of content, the style, grammar, and spelling will be checked by the writer and probably several other people within the company. But those producing spam and conducting phishing attacks don’t always have the finest grasp of the language. They will misspell words and their sentence structure might not make any sense. Make sure employees read all communications carefully and look out for errors.
- The Content Requests Personal Information
In an initial email to a client, a company will rarely ask for personal information to be provided. They might ask that the recipient subscribe to their communications or that they call company directly, but a bank, for example, will never require a customer to complete information via an email within its first initial communication. This is a common sign that the attacker is simply looking to extract as much information as possible from the target in the shortest amount of time.
- The Action Wasn’t Initiated by the Recipient
In cases where an email is received, and the initial contact was unsolicited, the communication is likely to be some form of spam. Legitimate companies will rarely send out first emails directly unless the recipient has signed up to a newsletter list or has agreed in some other way to the communication. For employees that receive emails seemingly out of the blue, it’s important to look closely for signs of a potential phishing scam.
- The Offer is Too Good to be True
We’ve all heard of the Nigerian Prince scam in which the recipient receives a letter from a member of the Nigerian royal family asking for a small loan, with the incentive of a large reward once the loan is paid. This is a clear example of a case in which the offer is too good to be true. A national lottery will not announce its winners via email. A long-lost uncle will not suddenly appear via email ready to give away their millions of dollars. If the offer is unbelievable, it’s best to be ignored completely.
- The Message Contains Threats
One of the most common phishing scams involves a message purporting to be from a government agency detailing a very specific threat against you or a member of your family. The communication might involve the recipient owing money to the government. Or it might detail other illegal activity that the recipient is said to be involved in. Inevitably, the sender will ask for money to resolve the legal issue. It’s important to note that government agencies rarely send out email as their first form of communication and that threatening emails impersonating a government representative are an exceptionally serious crime in the US.
- Attached PDF files With Links in the PDF
An email will come in that has a PDF file attached and has passed all the scans. When the PDF is opened there will be a hyperlink in the PDF and that will take you to a malicious site.
Microsoft 365 with Duo
Loging on to Microsoft 365
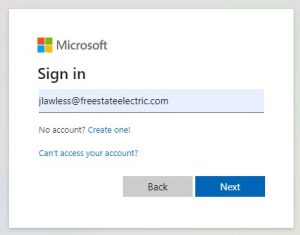
When logging into Microsoft 365 you will get prompted for your email address.
Microsoft 365 will NEVER prompt you for your email address and password in the same window. If you see both in the same window it is a Phishing attempt.
After entering your @freestateelectric.com email you will get redirected to Freestate’s login page. This page will also prompt you for your email address and have the Freestate logo at the top.

After entering your Freestate email address you will be taken to a password window that will also have the Freestate logo.

After entering your password, you may get prompted to authorize the login with a Duo push depending on the application you are logging into or your location.